On our blog, we often like to share helpful tips. From things like how to disable password logins on your server to setting up password aging policies.
One thing we've not explained is Why you shouldn't be using passwords and Why it's not a great idea to be manually adding SSH keys to your server.
Password authentication is really popular, and it's so easy to use. Most Linux distributions come with password-based SSH access enabled out of the box, so why wouldn't you use it if it gets the job done?
At any one time, there are tens of thousands of 'bots' trying to brute force access to servers via SSH. They automatically keep trying to break in, using common usernames such as 'root', 'ubuntu', and 'user'.
They'll even try obscure services that are known to create their user accounts, such as Nagios and Git. And then there are passwords. These days there are databases with billions of combinations of passwords, and you can guarantee bots are using them. That super secure password you used on all your servers? It's not going to cut it.
Of course, there are a few things you can do to protect your server. You can change your SSH port, which immediately knocks out some of the more basic bots, but many of them will still keep trying. You can restrict logins to certain IP's such as your office, or even your own country, but that's still not foolproof. If a machine in your office is compromised then your servers may as well be too.
This pretty much rules out passwords ever being a good idea for any server that is web-accessible. Whatever reasoning or steps you try to take, the fact will remain that you are allowing someone - anyone, to provide two lines of text (a username and password) to get full access to your server, and the chances are there's little stopping them trying this over and over again until they get in.
Fail2Ban is a great tool, and you really should have it installed even if you aren't using password-based logins. When set up correctly it can help mitigate some fairly sophisticated attacks.
It does however only help reduce the frequency of attacks. In the age of cloud computing, IP address blocks aren't very effective against bots.
We've explained why passwords are generally a bad idea. The solution is to switch to SSH keys. SSH keys are great because it creates a unique pair of keys that can only ever work with each other.
On your server, you store the public part of the key. This is the part that doesn't need to be kept a secret, and if you've ever added a key to somewhere like Github or Gitlab you'll find they provide a URL so that anyone can access your public key.
The private key remains on your machine, and is never, ever shared. Then when you try and connect to your server your key essentially creates a two-way 'handshake' to verify who you are.
Using this method means that every person you want to be able to access your server has to explicitly be given access by you - you have to manually copy over the public part of their key to your server's user accounts before they can log in.
You're probably spotting the big issue here, and it's the reason people often cite for why they still use passwords. Managing SSH keys can be a real pain!
As you can imagine, or have possibly experienced, the more servers and team members you have the more often you find yourself having to add their SSH keys, and you can bet that when the person leaves the company their SSH key never gets removed.
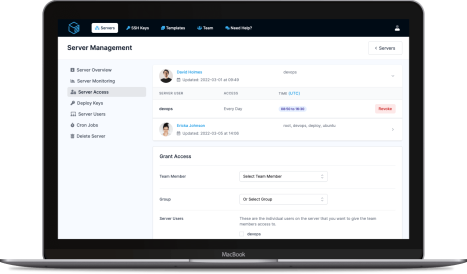
Here's where ServerAuth comes in. Instead of you having to manually log in to each server and add ssh keys all the time, the ServerAuth agent can do it automatically. Your team never even has to give you their keys, instead, you just invite them to your team and select the servers they can access. When they add or change their ssh keys ServerAuth automatically updates them across all of your servers.
Our key aim with ServerAuth is to make securing SSH access insanely easy to manage, and as secure as possible.
From our quick 1 minute automated setup, to our security-focused infrastructure that ensures only the people accessing your servers are the ones you've allowed to.
And it doesn't stop there. By using ServerAuth you can schedule access. If you've got part-time staff, contractors, or team members who only need to access servers on specific days, or between certain hours, our scheduled access controls will allow you to further enhance your infrastructure security.
More Links & Features
ServerAuth provides a whole host of management tools, from controlling who can access your server, to managing your website deployments. And with an ever-growing suite of tools you'll always be one step ahead!
Start for free