Server security is never about one main thing to protect your server but many little tricks that all add up to help decrease the chances of your server being compromised. Disabling password login is one of those tricks, it helps protect you from those situations where your password may be compromised through phishing or simply having a weak password.
Before proceeding with this guide, make sure you have set up SSH keys on your server to allow you to login without a password. You will also need to make sure you are doing this as root or a user with sudo access.
Once you have your SSH keys set, swap out the placeholders and use the command below to login to your server.
ssh -p PORT username@hostname
The SSH Config file should be located within /etc/ssh and is named sshd_config. For this guide, I've used the editor "nano", but you can swap out nano for your preferred editor. To perform any actions on this file, you will also need to be logged in as root or prefix any commands with sudo.
sudo nano /etc/ssh/sshd_config
Once you have the config file open, search for the following three items and set them to no.
ChallengeResponseAuthentication no
PasswordAuthentication no
UsePAM no
After those three settings have been set, save & close the file. With nano, the shortcuts are CTRL + O, then ENTER to confirm and save the file. Then CTRL + X to close the file.
As with most things on a server, SSH needs to be restarted before the changes can take effect. How to do this can depend on the flavor of Linux you are running, here are some of the common ways to do this, find the one that works on your server:
sudo service ssh restart
sudo systemctl restart ssh
sudo /etc/init.d/sshd restart
To test this has all worked, it's recommended that you keep your current terminal window logged in, and open up a new one to test. This is so that if something unexpected has happened you are able to revert the changes.
ssh -p PORT username@hostname -o PubkeyAuthentication=no
Remembering to swap out the port, username & hostname. You will notice the addition of -o PubkeyAuthentication=no, this tells your computer to not use your SSH public key to attempt the login with. This will ordinarily result in the server asking you to enter the SSH password however in our case this should result in a Permission denied (publickey) error.
It's worth noting here, don't throw out your passwords just yet! Your password will still be needed whenever you run any commands via sudo!
And that's it, your server is now configured to not accept passwords for logging in your server!
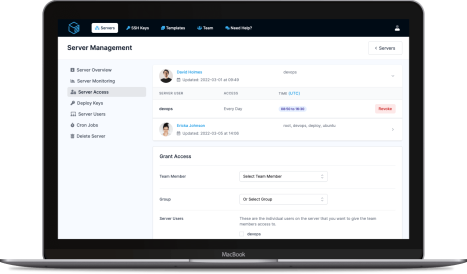
ServerAuth provides a whole host of management tools, from controlling who can access your server, to managing your website deployments. And with an ever-growing suite of tools you'll always be one step ahead!
Start for free